Siobhan Stands Out on Rolling Stones Night
 The first night out for the top 12 was dedicated to the Rolling Stones — you know, they
sing that Susan Boyle song, “Wild Horses.” I love that song!
The first night out for the top 12 was dedicated to the Rolling Stones — you know, they
sing that Susan Boyle song, “Wild Horses.” I love that song!
In fact, Katie Stevens chose to do the Susan Boyle song, and managed to come up with a new, power-ballad interpretation in a belting voice. The judges agreed this was her least problematic — which is to say, most successful — performance. “This is the first time I think you connected with a song,” said Simon. “Well done.”
The wildest moment of the night was Siobhan Magnus, made over in a sleek dress and curled hair, singing an intensely melodramatic cover of “Paint It Black.” The Judging Four were thrilled, especially when it ended with another of her roof-rattling shrieks. “Like Snooki’s pouf,” Ellen said, Siobhan had risen above everyone else. Kara thought it was the best turn of the night, and so did Simon: “The standout.” He added, however, that a lot of people would hate it.
That includes me. She looked like a French pop star struck by lightning.
Crystal Bowersox, the one singer you might have expected to have a knockout with this sort of blues-rock, didn’t quite connect with “You Can’t Always Get What You Want.” She just sort of strummed along, comfortably and even respectfully melodic, but the song didn’t build to anything. “This is the first time where I think you were beaten by somebody,” said Simon, “and that was Siobhan. … You’ve got to come on that stage, and you’ve got to kill.”
The disaster of the night? That would be Tim Urban. He sang a reggae “Under My Thumb,” perhaps trying to sound like early Police. The sexual aggression of the original was gone, and that left nothing. “I felt like I was at a resort and drinking a pina colada,” said Ellen.
Didi Benami cemented her comeback singing a slowed-down, sexed-up “Playing With Fire.” It didn’t really convey the threat of the lyrics — she’s not a singer who carries a lot of matches. But the judges were pleased. “Didi, you’re on fire tonight,” said Randy. Kara: “You got dark.” Ellen liked her phrasing: “You made the word ‘fire’ two syllables, which I thought was gr-eat.”
Casey James had rollicking fun doing “It’s All Over Now” with his electric guitar. Ellen made a cute little joke about not being about to appreciate him as a straight sex symbol — that his appeal doesn’t work for “people like me … blonds” — but she thought he was “fantastic.” Simon carped that it felt like an audition — Casey wasn’t pushing himself. “There’s got to be more.”
Lacey Brown sang “Ruby Tuesday” to a stupid string arrangement that made it sound like the Beatles’ “Eleanor Rigby.” Ellen thought it was “a tiny tiny bit sleepy.”
Andrew Garcia took “Gimme Shelter,” with its rumblings of danger, and turned it into something like a lounge performance in the shadow of the apocalypse. The judges were split. Ellen called it his “best performance yet.” When Kara complained that he had defanged the song’s imagery of war, Simon countered: “Did you want him to come onstage with a tank?” Well, yes.
Lee Dewyze’s version of “Beast of Burden” particularly impressed Kara (“You are growing faster than anybody… Tremendous growth”) and particularly frustrated Simon — he thinks Lee has yet to have that big “moment” of onstage electricity, and should. He does have a way of just … standing there.
Paige Miles, who’s had a troubled run up to now, nonetheless happens to have a very good voice — and despite laryngitis, and hardly any rehearsal, still pushed her way through “Honky Tonk Woman.” The judges seemed to think she’d at least recovered some of the ground that had been slipping away in recent weeks. ENOUGH ground, though?
Aaron Kelly, in a simple, understated performance, managed to capture the tender sadness of “Angie.” The judges all ranked it as one of his best nights yet.
Michael Lynche was confidently smooth on “Miss You.” Kara, invoking Mick Jagger himself, praised him for being “hot onstage.” Simon, though, cautioned that his moves were a bit corny and “a tiny bit desperate.”
This led to a weird faceoff between Simon and Ryan.
Ryan asked Simon to clarify his criticism and Simon, in effect, told Ryan to mind his own beeswax. Ryan at that point marched down off the stage, leaned across the judges’ table and tersely informed Simon he was just trying to make it clear that Michael understood Simon’s critique. “I’m actually trying to help out a little, buddy,” he told Simon, as if they were having an altercation in a diner. Simon waved him back toward the stage.
What on earth did any of it mean?
Most in danger: Tim, Andrew, Paige, Lacey.
Reblogged via Tom Gliatto for People.com
9:33pm, 17 March 2010.
Manny Pacquiao’s Secret to Success
The twenty-first century’s greatest boxer got to be that way because he knows what Ali knew: There’s nothing wrong with having a little fun. Intimate moments with the little man who, after another title fight on Saturday, can’t get much bigger than this.

Courtesy of Jed Jacobsohn/Getty
“I don’t care who trains Joshua Clottey for this fight — he can’t beat us,” trainer Freddie Roach said before Saturday’s fight. “I go for a kill at all times.”
ARLINGTON, Texas — Manny Pacquiao began this past Saturday at a morning Mass — the medieval Spanish Catholic kind that borders on mystic, the kind that blesses a boxer’s gold groin protector in front of five-hundred Filipinos like it were a newborn. He ended it not having needed much blessed protection from anything, a puffy eye the only residue from a pummeling — and I think 1,231 punches, including one 36-hit combination I counted from ringside, counts as a pummeling — of Joshua Clottey to retain the welterweight championship of the world.
What he needed was another helping of tinolang manok — the chicken-broth soup with special leaves from his native Philippines that he eats for almost every meal, that has bulked him up through seven different weight classes, all of which he has dominated and another one of which he could probably conquer, too. But there he was, all 5’6″ and 145 of him: the greatest and unlikeliest pound-for-pound fighter in the world, standing in the middle of Cowboys Stadium on the receiving end of some Texas-style pageantry, loving every second of it. “Michael Irvin has an aura — he had a way to create energy,” Jerry Jones told me. “Manny has that. I know what ‘it’ is. It’s taking a talent and maximizing that talent and walking the walk. That’s what he is: He walks in, and has that aura.” Ross Greenburg, president of HBO Sports, likened him more to Ali. “Reminds me of a time I was walking with Muhammad Ali and he literally stopped traffic,” he told me. “People were mesmerized, and it is the same with Manny.”
That’s because Manny Pacquiao likes to have a good time. Good times are what make him so good. He is the lead singer in a band that, despite its lead singer’s high-pitched crackle of a voice, has sold more than a million albums. (His trainer, Freddie Roach, has invoked a 9 P.M. “karaoke curfew” leading up to fights.) He is in the best shape of his life, despite what rival Floyd Mayweather Jr. would have you believe. (“He is accusing me of using drugs or whatever and trying to ruin my name in boxing,” Pacquiao says. “Maybe he is afraid of me or maybe is not ready for this fight.”) He is running for Congress back home, despite the fact that 21 people were killed on their way to file candidacy papers four months ago in the kidnap-happy Philippines. (“He’s a rock star, but he’s still hungry,” Roach says.)
All this laughing from a 31-year-old man who beats up people for a living and comes from, well, shit, and kind of still likes it that way. Pacquiao’s father, having already eaten the family dog, abandoned his family, leaving Manny to stow away on a boat headed for Manila, where he barely made enough money as a laborer to buy a daily bowl of rice. At 16, he found a degree of solace at a 24-hour boxing gym, if only because it smelled a bit less like sweat than the construction site where he worked and slept. Now, despite the Beverly Hills mansion where he lives with his wife and four children, Pacquiao shacks up with fourteen other men at a small apartment during training camp. A couple of guys sleep right at the foot of his bed. Good times.
Good times are especially important right before a big fight. Like the last two months — much of which I’ve spent by his side, too — when his practice boxers pretended to be Joshua Clottey, Saturday nights’s opponent. In the Wild Card Boxing Club, a dank Los Angeles gym with old newspaper clippings plastered to the walls, the sparring partners would come forward and hit Pacquiao, if only for him to try out his new line: Bababababababa came the scream, and then ratatattat came his fists’ counterattack. One day another guinea pig dealt him a low blow. Pacquiao tends to bite his lower lip and pound his gloves together when he’s hurt, but this time he just knocked the guy silly — so silly the guy could barely talk fifteen minutes later. I asked Roach, the head trainer, how hard Pacquiao really works in sparring sessions. “Maybe sixty percent,” he said. “He can fuckin’ hit.”
Pacquiao likes to play basketball (he owns a team), play poker (he sponsors a tournament), chat endlessly on his cell phone (“Manny, Mike Tyson wants to talk to you.”), and work on that croon of his with a voice coach (she often tells him to warm up his tongue by rolling his r’s like a crazed cricket), but he mostly spends his days at the gym. His trainers have a difficult time slowing him down: up early to run a few miles and do sprint work at a Los Angeles public high-school track, followed in the afternoon by a grueling three-hour workout with heavy bag work, sparring, plyometrics, shadow-boxing, jump-roping, work on the speed bags, and some other guy hitting him with a bamboo pole. One of those other guys is Buboy Fernandez, a childhood friend whom Pacquiao found homeless on the street one day and turned into a trainer. Other other guys hold his comb, take care of his diamond earring, fluff his rice, hang up his exercise mat, and walk his Jack Russell terrier, named Pacman. All this and a lot of winking from a man who has only been boxing professionally for fifteen years and speaking English for four but still loves to yell “Fuck you!” at his fitness trainer after stomach crunches. That’s probably because he does 1,400 of them a day. He starts every round by crossing himself, and ends every training session with a prayer. On Sundays, Manny rests.
On Saturday night, of course, he was pretty relaxed anyway. Roach, a four-time trainer of the year and not a bad fighter himself, told me he’d never seen a boxer this happy this close to a title bout. I couldn’t help but believe him: Here was a young man who used to sell doughnuts on Manila street corners making bad jokes for his buddies as he wrapped his own hands in tape so tight they were practically purple — while the Dallas Cowboys cheerleaders were checking him out. (They also sung the national anthem.) “But when he enters the ring and crosses himself,” Roach reminded me, “it’s all business.” And it was. From ringside, you could barely even follow Pacquiao’s red gloves, made from leather and woven horsehair, they were moving so fast. Clottey actually chose a particular type of padded glove just to help defend his face — not that he went down, but not that he stood much of a chance in the decision either. “He is fast. He is fast,” Clottey said after the fight. “He is strong, too.”
Pacquiao, for his part, already had his sunglasses back on as his guys sped him off back to Mass. There was no time to waste, after all: His band had a big show on Saturday night, too. Boxers never like to go to bed early because that much unencumbered adrenaline running through a man’s system can kill him. Pacquiao told me his first song would be “La Bamba,” and that the concert would go well into the night.
Reblogged via Esquire by Gary Andrew Poole who has written for The New York Times, Time, and The Atlantic. He is writing a biography of Manny Pacquiao.
10:39pm, 15 March 2010.
The Milestone
It’s finally here! My new Motorola Milestone, fresh from Hong Kong.
A couple of months ago, I asked my good friend, Dick, who’s a resident of HK to look around for iPhone 3GS prices for me. There is one place in HK where you can get unlocked iPhone 3GS, Fortress, the one-stop electronic superstore. iPhones were priced at HK$ 4,288 – 8GB, HK$ 5,388 – 16GB and HK$ 6,288 – 32GB respectively. With this in mind, I had my eyes set on the 16GB.
Come 6th of March, my friend went to Fortress at Tung Chung Mall finally get the iPhone 3GS. Bad news. All out of stock. The reason: a local carrier unveiled an über-low call & data plan. Hongkees swarmed the shop and grabbed all the iPhones they can get.
With quick thinking, I went for the Milestone. This was my third choice from my recent blog. The Nexus One was available online in Hong Kong, but I didn’t want to trouble my friend with all the fuzz. So Milestone it is. The good thing, it’s a steal! HK$ 4,680 for it’s specs and build, wow!
What’s in the box:
1. Motorola Milestone
2. Battery
3. USB Cable
4. Power Adapter
5. 8GB microSD card (already fitted in the Milestone)
6. 3.5mm Wired Stereo Headset
7. Software CD
8. User’s Manual
Time to explore the Android OS. Let the good times roll.
5:43pm, 13 March 2010.
Leave No Trace: How to Completely Erase Your Hard Drives, SSDs and Thumb Drives
With stories abounding of identity theft aided by information lifted from discarded storage devices, you want devices you no longer plan to use to have no usable information when they head out the door. Here’s how to wipe them clean.
Why Erasing Files Is Not Enough
Sure, you could erase the contents of the drive, but keep this in mind: the act of erasing a file does not remove it from a storage device.
When you erase/delete a file from your computer, it’s not really gone until the areas of the disk it used are overwritten by new information. If you use the normal Windows delete function, the “deleted” file is sent to the Recycle Bin until the space it uses is required by other files. If you use Shift-Delete to bypass the Recycle Bin, the space occupied by the file is marked as available for other files. However, the file could be recovered days or even weeks later with third-party data recovery software. As long as the operating system does not reuse the space occupied by a file with another file, the “deleted” file can be recovered.
With SSDs, the erased file situation is even more complex. SSDs store data in blocks rather than in sectors as with magnetic storage. Overwriting a block was previously used involves copying the contents of the block to cache, wiping the block’s contents, delete the block to be overwritten from cache, writing the new data to cache, and rewriting the block with the new data. As an SSD is used with files that are deleted or changed frequently, the performance can drop unless the drive (and operating system) support a technology called TRIM that wipes out deleted data blocks as soon as the file using the blocks is deleted. TRIM is supported by Windows 7 and by some late model SSDs, but not by older Windows versions. So, disk wiping can be both a security feature and a performance improvement strategy.
Data Wiping Versus File Erasure
While erasing files simply marks file space as available for reuse, data wiping overwrites all data space on a storage device, replacing useful data with garbage data. Depending upon the method used, the overwrite data could be zeros (also known as “zero-fill”) or could be various random patterns.
Products that can be used for wiping hard disks might not be suitable for wiping other types of drives. In this article, we will look at methods for securely wiping hard disks, USB flash memory devices, flash memory cards, and SSDs.
Zero-Fill a Hard Disk
Time Needed: several hours (varies with size and speed of drive)
Software: Hard disk utility software from your drive vendor
Media: blank CD or floppy disk
Although writing zeroes across the entire hard disk surface (aka “zero-filling”) is not sufficient to meet government data sanitation (disk wiping) standards such as DoD 5220.22-M or the more comprehensive Standards and Technologies (NIST) Special Publication 800-88, overwriting the entire hard disk prevents most types of data recovery from being successful.
Here’s where to get zero-fill software from hard disk vendors:
Hitachi
Drive Fitness Test (see website for specific models supported)
http://www.hitachigst.com/hdd/support/download.htm#DFT
Select the Erase Drive feature to zero-fill your hard disk

Samsung
HUtil (see website for specific models supported)
http://www.samsung.com/global/business/hdd/support/utilities/Support_HUTIL.html
Use Tool, Erase HDD to zero-fill your hard disk

Seagate (including Maxtor)
SeaTools for DOS (see website for specific models supported)
http://www.seagate.com/www/en-us/support/downloads/seatools
Use Full Erase to zero-fill your hard disk

Western Digital
Data Lifeguard Diagnostics (select drive model for specific version recommended)
http://support.wdc.com/product/download.asp?lang=en
Use Write Zeros to drive to zero-fill your hard disk

1. Determine the brand and model of hard disk you want to overwrite.
2. Download a CD ISO image or a floppy disk image (depending upon your equipment) and use the image to create bootable media. The floppy disk image is self-contained: run it, insert a blank floppy disk when prompted, and the image is created on the disk. You will need to use a CD burning program that works with ISO images to convert the ISO image into a bootable CD.
3. Restart your computer with the bootable media you created in Step 2.
4. Select the hard disk to zero-fill when prompted.
5. Choose the option to zero-fill the hard disk.

6. When the program is finished, follow the on-screen instructions to shut down or restart your computer.
7. Remove the wiped hard disk; you can now reuse or recycle the hard disk.
Secure Wiping a Hard Disk
Secure wiping goes beyond zero-fill operations, and provides an extra level of security. Most secure wiping programs are designed to meet DoD 5220 standards, which require three passes of overwriting with a special numeric pattern and verification. More information about this and other secure standards are available from the DataErasure website.
(Note that the 2007 revision of the Defense Security Service, Updated DSS Clearing and Sanitization Matrix (June 28, 2007) (PDF) now recommends degaussing or drive destruction for maximum protection.

Stanford University’s Disk and Data Sanitization Policy and Guidelines, a must-read for understanding data wiping issues, recommends Darik’s Boot and Nuke (DBAN) for secure hard disk wiping.
Secure Wiping a Hard Disk with DBAN
Time Needed: several hours (varies with size and speed of drive)
Software: Darik’s Boot and Nuke (DBAN); available from http://www.dban.org/
Media: blank CD (all versions) or floppy disk (version 1.0.7 and older versions)
1. Download the DBAN boot image ZIP file (we used version 1.0.7 and beta version 2.0 for this article); we downloaded the ISO image for CD burning, but a floppy disk builder is also available
2. Extract the contents of the compressed file.
3. Burn the ISO image file extracted in Step 2 to CD; see our article on how to do this, or use the built-in ISO CD image burning support in Windows 7. If you downloaded the floppy image builder, run the program to create a bootable floppy disk.
4. Restart the computer using the CD or floppy disk created in Step 3.
5. Press Enter to run DBAN in interactive mode.
6. Use up and down arrow keys to highlight the drive to wipe.
7. Press the space bar to select the drive.
8. Press M to select the wiping method.
9. Press F10 to begin the wipe process.

10. At the end of the process, shut down the system. You can reuse or recycle the wiped hard disk.
Note: if DBAN is unable to recognize your SATA hard disks, configure your system BIOS to use IDE mode rather than AHCI mode.
Wiping Flash Memory Cards and USB Drives
Programs such as DBAN or vendor-supplied hard disk utilities are limited in the devices they support: they are designed to work with internal ATA/IDE or SATA hard disks only. Programs that work with flash memory cards and USB flash drives often support hard disks as well, enabling you to use a single program for all disk wiping processes. Roadkil’s DataWipe can be used with any hard disk, floppy disk, or flash drive that has a drive letter.
Wiping Flash Memory Cards with Roadkil’s DiskWipe
Time Needed: Varies; from a few minutes to several hours, depending upon size and speed of drive and computer
Software: Roadkil’s DiskWipe, available from http://www.roadkil.net/
Media: Can be run from Windows desktop
1. Download Roadkil’s DiskWipe.
2. Extract the contents of the compressed file.
3. Open DiskWipe. If you are running Windows Vista or Windows 7, right-click the program icon and select Run as Administrator.
4. Select the drive to wipe.
5. Select the type of wipe to perform; DiskWipe can zero-fill the disk or write random data.
6. Enter the number of passes.
7. Click Erase to start the process.

8. At the end of the process, close the program. You can reuse the wiped disk.
Wiping SSDs
To solve write performance problems on drives that don’t support TRIM (check with your drive vendor for firmware upgrades) is to use wiper.exe (included with some SSDs) or to run the Secure Erase feature supported in most recent ATA/IDE and SATA drives. The Secure Erase feature can be activated on many systems by running Secure Erase 4.0 (HDDerase.exe), available from http://cmrr.ucsd.edu/people/Hughes/SecureErase.shtml. Version 4.0 works with most recent ATA/IDE and SATA hard disks and SSDs, but if you use an Intel X-25M, X-25E, or X-18M SSD, follow this link to download Secure Erase 3.3 http://www.iishacks.com/index.php/2009/06/30/how-to-secure-erase-reset-an-intel-solid-state-drive-ssd/. Note that it is no longer being developed, and we were unable to use it on a system running an AMD 690 chipset.

Wiping Drives and Free Space with SDelete
SDelete is a free program from Microsoft’s TechNet Sysinternals collection. It runs from the command line, and can be used to wipe drives, wipe files, or wipe free space.
Time Needed: Varies; from a few minutes to several hours, depending upon size and speed of drive and computer
Software: TechNet Sysinternal’s SDelete, available from http://technet.microsoft.com
Media: Can be run from Windows desktop
1. Download SDelete.
2. Extract the contents of the compressed file.
3. Copy sdelete.exe to c:\windows\system32\ (this will enable you to run it from any location)
4. Open a command prompt session with Administrator rights.
5. To wipe all files on drive X: and its subdirectories and to wipe free space, enter Sdelete -p 2 –s -z X:\*.* (to see all command-line switches, enter Sdelete with no options)
6. Wait; the program displays status messages as it runs. When the program is finished, you can reuse or dispose of the drive.

Evaluating the Effectiveness of Disk Wiping Programs
We used demo versions of two popular data recovery programs to evaluate some of the disk wiping programs discussed in this article. To determine whether a typical data recovery program could recover files on a SD card wipe with Roadkil’s DiskWipe, we first of all formatted the card using a card reader. Ontrack’s EasyRecovery Data Recovery (available from http://www.ontrack.com) had no difficulty finding folders and files to retrieve.

However, when we used DiskWipe to wipe the drive using a one-pass blank disk (zero fill) operation, EasyRecovery DataRecovery was unable to find the file system, let alone any files or folders.
After reformatting the card, taking a few photos, and deleting the photos, EasyRecovery Data Recovery was able to find the new photos, but the contents of the card before running WipeDisk were unrecoverable.

To evaluate SDelete, we used SDelete to wipe all of the files on a hard disk, but omitted the –z switch; when –z is not used, SDelete deletes files and renames them, but does not clear free space. To determine what might be visible, we used a demo version of Disk Doctors NTFS Data Recovery software, available from http://www.diskdoctors.net.
Disk Doctors were able to locate the deleted folder and Outlook Express message folders, but SDelete had renamed them from their original names and DBX extensions (Outlook Express message folders). If you use SDelete, it’s very important that you take time to use the –z switch to clear free space on the disk (once a file is deleted, the space it occupies is free space).

We also used Disk Doctors to evaluate the effectiveness of a freeware program called Eraser, which can delete and overwrite files and folders from the right-click menu. We created a documents folder with a subfolder called Figures and used Eraser to overwrite the folder and subfolder using its default settings.
Disk Doctors was able to locate the folders, but the contents are files with garbage names and are zero bytes in size – except for leftover word processing temporary files (files that begin with $). These filenames were not changed, which could enable a snooper to figure out the names of the files in the folder – although the files themselves were destroyed. By using more overwrites or different methods available with Eraser, a more thorough wiping may be possible.

Conclusion
We’ve highlighted a variety of free ways to protect data on castoff drives from being retrieved. As you can see, your best bet is to overwrite data directly, but you also might want to consider using a program such as SDelete to scramble filenames first and then use a disk wiper such as Eraser or WipeDisk to finish the job.
Use demo versions of data recovery programs such as Ontrack Easy Recovery Data Recovery, Disk Doctors Data Recovery (various editions for NTFS, FAT, and flash media), and others to evaluate the effectiveness of your data wiping procedures. Remember, the full versions of these and other data recovery programs can save your data if you accidentally format or partition a disk because, until the data is overwritten, it’s still there.
Reblogged via Gizmodo
11:43pm, 10 March 2010.
Up in the Air
Friday Night Movie of the Week: Up in the Air

Courtesy of Paramount Pictures
Starring:
George Clooney as Ryan
Vera Farmiga as Alex
Anna Kendrick as Natalie
Synopsis:
Corporate downsizing expert/challenge speaker Ryan Bingham’s traveler lifestyle is threatened by a feisty newcomer Natalie Keener who singlehandedly developed a new scheme of firing people, through the internet. Along the way, he meets Alex Goran, another frequent-flyer, whom he develops instant chemistry. Truly, the story of a man ready to make a connection.

Courtesy of Paramount Pictures
Ryan shows young Natalie how it is done the natural way, canning people in their face.

Courtesy of Paramount Pictures
Ryan meets Alex in one of his numerous membership only VIP lounges. Strikes a conversation about their rental car service preference. Each flashes their VIP membership cards. Bonds perfectly.

Courtesy of Paramount Pictures
One of the funnier moments of the film happens when he takes snaps of this cut out photo of his sister and fiancé wherever he lands. Later on, he rewards the couple 500,000 miles flyer miles each as a wedding present.

Courtesy of Paramount Pictures
Heartbreak and Natalie leaving his firm leads our hero back to what he loves, flying. He reaches his dream of 10 million frequent flyer miles. The seventh to do so.
Review:
This Oscar nominated film was character driven, specifically the three major roles. Clooney being Clooney. Not really acting for him, he was just being himself. A long shot for him to take Oscar gold as lead actor. Some funny moments here and there. Anna Kendrick of Twilight fame, was the bright light of the movie. Quirky funny. Vera Farmiga did better in The Departed. The only thing I remember of her presence in this movie was when she flashed her nice buttocks for a couple of seconds. I loved the overhead city shots with the name of the city. Very retro.
Plot was predictable but being unpredictable is not the purpose of its screenwriter and director. On a side note, I kept telling Abbie that the character Alex is married and I was right. The tell was her hair. Most married women wear their hair that way.
Rent it. Nothing special in the movie houses.
1:46pm, 6 March 2010.
Rest Day
Everybody needs one. I know I do. After last week’s three-day seminar-workshop followed by a couple of rush presentations for the central and regional management conference, rest is paramount in my to-do list. Battling bad dry cough since Saturday added to my anguish.
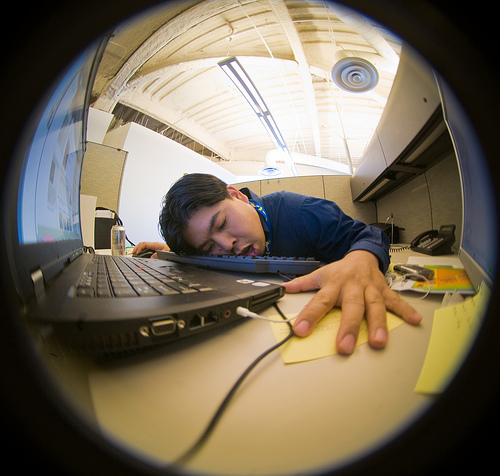
Courtesy of arkworld
My boss just called me on my mobile. She asked how was I doing? How and where was the presentation? And wished me well. Beginning to be a stress-less day 🙂
Take one too.
10:10am, 4 March 2010.
Sync data with Macs, iPhones using Google
Keep your contacts and calendars up to date in multiple places for free
If you have two or more Macs, or an iPhone or iPod touch, you’ll undoubtedly want to keep your contacts and calendars on all your devices in sync. One way to do so is to use Apple’s MobileMe service ($99 a year for individuals; $149 for the five-user Family Pack). With MobileMe properly configured on each of your devices, any change you make to contact or calendar data syncs almost instantly with the other devices (and, in the case of the iPhone, syncs over the air).
But what if you don’t want to pay for MobileMe, or if you simply prefer using the free Google Contacts and Google Calendars (both accessible from any Gmail account)? Google lets your iPhone or iPod touch connect to your Gmail account (either with a gmail.com address, or an address at your own domain via Google Apps) using Exchange ActiveSync, which provides over-the-air push e-mail, contact, and calendar data, just as MobileMe does. Meanwhile, Snow Leopard contains native support for Exchange 2007 servers in Mail, Address Book, and iCal, and Microsoft Entourage also supports Exchange accounts. So in theory, one should be able to store contact and calendar information in Google’s cloud, access it using your existing software, and configure all your devices in such a way that everything stays automatically in sync.
Unfortunately, it’s not quite that simple. Although the iPhone and iPod touch work well with Google’s Exchange services, the same isn’t true of current desktop Mac software. You can sync your Google Contacts and Calendars with Address Book and iCal, respectively, but not using Exchange. As a result, syncing isn’t instantaneous or automatic. Likewise, Entourage can tie into OS X’s Sync Services to achieve syncing with Google Contacts and Calendars in a roundabout way, but setting up your Gmail account in Entourage as an Exchange account doesn’t work.
Nevertheless, you can replicate most of what MobileMe offers for contact and calendar syncing using Google’s services and Snow Leopard. The initial setup process is more complicated than with MobileMe, and you’ll have to adopt slightly different habits, but the end result should meet most people’s needs.
However, I do want to mention a few qualifications up front. First, the process I describe here is for syncing a single person’s data among multiple devices, not for syncing information among multiple users. Second, on an iPhone or iPod touch, this procedure uses Exchange, but the iPhone OS currently supports only one Exchange account per device. So, if you already use Exchange for another purpose (such as connecting to your corporate e-mail account), this solution won’t work. And third, although most contact and calendar data syncs between Mac applications and Google just fine, a few items (including Address Book groups and the “floating” time zone in iCal) do not.
Preliminary steps
Before changing your sync settings, you should perform a few preliminary steps.
First, be sure to back up your contact and calendar data so that if anything goes wrong, you can restore it to its previous state. To back up the contents of the OS X Address Book, open Address Book (in /Applications), choose File -> Export -> Address Book Archive, enter a name and choose a location for the exported data, and click Save. To back up your iCal calendars, open iCal (in /Applications), choose File -> Export -> iCal Archive, enter a name and choose a location for the exported data, and click Save. To back up your Entourage contacts and calendars, open Entourage, choose File -> Export, select Items To An Entourage Archive and then All Items. Also, in the Archive The Following Items Types section, select the Local Contacts and Local Calendar Events items (you can deselect the other checkboxes) and click the right arrow. Leave the No, Keep The Items In Entourage After They Are Archived option selected and click the right arrow again. Enter a name and choose a location for the exported data, and click Save. If you’re using an iPhone or iPod touch, attach it to your Mac using its USB cable or dock and allow it to sync before proceeding.
In addition, if you’re using Google Apps (for a custom domain name), make sure you’ve enabled Google Sync for your domain by following Google’s instructions.
Finally, if you are a MobileMe user, I suggest turning off MobileMe syncing for contact and calendar data, as that will simplify setup and troubleshooting. To do so on your Mac, open the MobileMe pane of System Preferences, click the Sync tab, and deselect the checkboxes for Contacts, Calendars, or both. On an iPhone or iPod touch, go to Settings -> Mail, Contacts, Calendars, tap your MobileMe account, and turn Contacts, Calendars, or both off. When you do so, your device asks whether you want to keep or delete the existing contacts or calendars on your device. The safest option is to tap Keep On My iPhone, but due to the way Google stores information, this may result in some duplicated contacts or events. If you’re certain that the data on your Mac is correct, up-to-date, and backed up, you can reduce the chance of duplicates by tapping Delete From My iPhone.
Sync contacts with Address Book
To sync Address Book with Google Contacts’ My Contacts list, open Address Book, choose Address Book -> Preferences, click Accounts, select On My Mac in the Accounts list on the left, and then click the Account Information tab. Select the Synchronize With Google checkbox, and then click Configure. If you’re setting up Google syncing for the first time, an alert appears explaining about the synchronization process; read this and click Agree. Then, in the dialog box that appears, enter your Gmail address in the Google Account field and your password in the Password field, and click OK. You may see a warning that Address Book can’t verify the identity of the server; if so, click Continue.
Next, make sure the Sync menu (an icon with two arrows arranged in a circle) appears in your Mac’s menu bar. If not, open the MobileMe pane of System Preferences, click the Sync tab, and select the Show Status In Menu Bar checkbox at the bottom. Choose Sync Now from the Sync menu. During the initial sync, if the Conflict Resolver window appears, click Review Now, decide which version of each contact to use, and then click Sync Now. After the first sync, OS X should sync changes once per hour, although you can sync manually at any time by using the Sync Now command. (If hourly syncing is too infrequent, you might try the $25 Spanning Sync, which syncs every time you modify a contact, and as often as every 10 minutes otherwise.) Repeat this procedure with each Mac you want to sync.
Sync calendars with iCal
To sync iCal with Google Calendar, open iCal, choose iCal -> Preferences, click on Accounts, and click the plus (+) button. Choose Google from the Account Type pop-up menu, and enter your full e-mail address (whether ending in @gmail.com or your custom domain) in the Email Address field and your password in the Password field, and click on Create. You may see a warning that iCal can’t verify the identity of the server; if so, click Continue. Your primary Google calendar then appears in iCal. To sync additional Google calendars, click the Delegation tab in the Preferences window and select the Show checkbox for one or more calendars.
Note that this entire procedure syncs existing Google calendars with iCal, but not the other way around. To move your existing iCal data into Google Calendar, find one of your calendars in Google on the left side of the screen, click the Settings button beneath it, click Import Calendar next to the Create New Calendar button, and then in the dialog box that appears, click Browse, navigate to the iCal backup file you created earlier, and select it. In the Import Calendar dialog box, select the calendar to which you’d like to add the events (if you have more than one) from the Calendar pop-up menu and then click the Import button to bring your calendar info in.
By default, iCal syncs with Google Calendar every 15 minutes, but you can change the interval if you prefer. To do so, click on the Account Information tab in the Preferences window and choose a new value from the Refresh Calendars pop-up menu. As with contacts, repeat this procedure on each of your Macs.
Sync contacts and calendars with Entourage
If you use Entourage to store your contacts and calendars, you can’t sync directly with Google Contacts and Calendars, but you can sync indirectly. First, follow the procedure for setting up syncing with Address Book or iCal and Google Contacts or Calendars (even if your OS X Address Book or iCal is empty).
Then, in Entourage, choose Entourage -> Preferences, select Sync Services under General Preferences in the list on the left, select Synchronize Contacts With Address Book And MobileMe and/or Synchronize Events And Tasks With iCal And MobileMe, and then click OK. In the dialog box that appears, read the descriptions of the three options for your initial sync (Combine Information, Delete Entourage Information, or Delete Information From Macintosh Address Book, iCal, And MobileMe), select the one you want, and click OK. (In most cases, if you use only Entourage for contacts and calendars, the best choice is Delete Information From Macintosh Address Book, iCal, And MobileMe.)
Sync contacts and calendars with an iPhone or iPod touch
To sync your contacts and calendars, you must be using iPhone OS 3.0 or higher. Go to Settings -> Mail, Contacts, Calendars and tap Add Account at the bottom of the Accounts list. Tap Microsoft Exchange, enter the full e-mail address associated with your Google account in the Username field and your password in the Password field; leave Domain blank. Tap Next. If an Unable To Verify Certificate message appears, tap Accept. In the Server field, enter m.google.com, and tap Next again. Make sure Contacts and Calendars are turned on (plus Mail, if you want to sync your Gmail e-mail) and tap Done. When prompted to choose how to handle existing data, tap Delete. Synchronization begins momentarily, and everything happens wirelessly.
Reblogged via Joe Kissell, Macworld.com
11:54pm 3 March 2010.
Jailbreaking in the iPhone 3.0 era
In a few short years, Apple has established the iPhone as the mobile platform to beat. Each successive firmware update opens new, and often unmatched, features for users and developers to explore. Many of these features, however, find their roots outside Apple’s walled-garden approach to the iPhone, as the jailbreak community proves time and again to be an innovative environment for off-limits apps that demonstrate new ways to push the iPhone platform forward.
To be sure, the past year of Apple updates has altered the pre-3.0 iPhone jailbreaking landscape. The company’s iPhone 3.0 OS, together with its speedy, feature-enriched iPhone 3G S handset, has brought new software and hardware capabilities that somewhat mitigate the need for jailbreaking. But despite these advancements, as well as warnings that jailbreaking leads to security risks and potential copyright infringement, iPhone jailbreaking continues apace, evidenced by the growing variety of rogue apps available for jailbroken iPhones.
Central to that growth is ongoing developer and user frustration with Apple’s enigmatic app acceptability rules, as well as its deliberate hobbling of many application capabilities, such as Web browsing, background processing, voice services, and tethering (in the United States). Jailbreaking also allows users to unlock their iPhones from Apple’s exclusive AT&T wireless service contract, freeing them to use their phones on other cellular providers’ networks worldwide. These factors, as well as developers’ interest in pushing the limits of the iPhone’s evolving capabilities, make for a jailbreaking community that is as vibrant as ever.
iPhone OS 3.0: Apple unlocks some features, keeps rein on others
Apple’s iPhone OS 3.0 opened the iPhone to several features previously available only to jailbroken devices: copy/paste, MMS, push notification, voice recording, global search, HTTP streaming, and peer-to-peer networking. Apple’s June release of the iPhone 3G S extended the iPhone’s hardware capabilities to include an enhanced camera, integrated magnetic compass, video recording, augmented reality and navigation, and voice control.
There were other signs that Apple might begin lifting restrictions on previously forbidden application categories. Yet it took a very public investigation by the FCC following Apple’s hobbling of Skype and rejection of Google Voice for the iPhone to persuade Apple and AT&T torelent on VoIP telephony. And though apps such as Google Voice and Skype can now be used on the device, limitations still abound. Internet tethering, an intensely desired feature, is one high-profile example. Built into OS 3.0, the capability remains restricted in the United States by monopoly iPhone carrier AT&T.
Meanwhile, Apple has not altered its SDK restriction on interpreted code, which rules out Flash and Java applications (although Adobe purportedly has a Flash work-around), as well as Flash video playing inside the iPhone’s Safari Web browser. Web browsers themselves remain off limits as an app category, except for simple repackaging of the iPhone’s built-in Webkit HTML rendering engine.
Then there are certain iPhone capabilities that Apple still reserves for itself: background processing, video recording on pre-3G S devices, application launching, video output, lockscreen and wallpaper customization, interface skinning, GPS tracking, and remote control of an iPhone from your desktop computer (a la Apple’s Mac OS X Screen Sharing).
Each of these limitations provides incentive for the jailbreaking community to thrive.
Apple’s ongoing objections to iPhone jailbreaking
Apple’s company line on the kind of features jailbreakers seek remains steadfast: These features reduce battery life, slow performance, introduce security vulnerabilities, stress the 3G network, and increase Apple support costs. It is under the auspices of these objections that Apple routinely blocks apps it doesn’t like from its App Store. Some developers argue, however, that often such blocking happens more for competitive reasons than out of concern for iPhone users’ safety and productivity.
Still, many of Apple’s concerns have in fact materialized in jailbroken apps. Background processing does reduce battery life and overall performance, according to users, but these same consumers say the feature is worth the hit as long as they can control its application. Battery drain is also a key symptom of a particular jailbroken-iPhone worm infection. Jailbreaking proponents, however, point out that the worm can only infect phones that users haven’t properly secured by changing the default password. As for stressing the 3G network, most signs point toregional differences in AT&T cellular data capacity as the root cause of this issue, as opposed to anything that jailbreaking would exacerbate.
Performance issues aside, Apple has registered its formal opposition to jailbreaking under the cloak of copyright, claiming the act is illegal under the Digital Millennium Copyright Act (DMCA). This claim has been disputed by the Electronic Frontier Foundation (EFF) and open source Web browser developer Mozilla, which has called Apple’s restrictions both harmful to innovation and an improper application of DMCA rules. Apple has thus far taken no legal action against users who jailbreak their phones, nor against any jailbreak-enablers, including the iPhone Dev Team, which has managed to jailbreak every iPhone OS update to date.
Meanwhile, the EFF and Mozilla have asked the U.S. Copyright Office for an exemption specifically permitting installation of legal apps on iPhones. The Office listened to arguments on both sides in a May 2009 hearing, but has missed its own October projection for a decision and has yet to issue its opinion.
Jailbreaking encourages iPhone innovation
Long before Apple launched its iPhone App Store in 2008, jailbreak users could download apps from a variety of repositories at a time when Apple limited customers to the apps it delivered with the phone. In fact, some argue that jailbreaking was instrumental in educating Apple about the shortcomings of its built-in apps, prompting it to launch the iPhone App Store to give developers an opportunity to fill the gaps.
Since then, Apple has demonstrated a pattern of recognizing features of interest in popular jailbroken apps, then addressing users’ desires for those features with OS updates. iPhone OS 3.0 follow-up updates have included features such as video archiving and editing, Bluetooth-enabled voice control, desktop-based application reorganization, pop-up blocking, wireless ringtone downloads, and remote handset locking and erasing, all of which originated in jailbroken apps.
Jailbroken apps may also have played a part in persuading Apple to loosen restrictions on certain application programming techniques that were previously disallowed, such as exploitation of so-called private API functions. In addition to concessions on VoIP apps, Apple has approved live streaming video apps such as Ustream Live Broadcaster and iPhone development aidiSimulate, both of which use private APIs.
Apple’s capriciousness drives developers to jailbreak
The iPhone’s 140,000 apps (and counting) continue to enrich both Apple and independent iPhone developers. Yet Apple’s uneven App Store administration threatens to kill, or at least maim, the app cash cow, despite recent signs of flexibility from Apple. In November 2009, Apple drove away major iPhone developer Rogue Amoeba after repeatedly rejecting its Airfoil Speakers Touch 1.0.1 app update. Rogue CEO Paul Kafasis said in his corporate blog, “Rogue Amoeba no longer has any plans for additional iPhone applications, and updates to our existing iPhone applications will likely be rare. The iPhone platform had great promise, but that promise is not enough, so we’re focusing on the Mac.”
But if high-profile defections such as Rogue’s threaten to undermine the breadth or quality of apps on offer at the App Store, Jay Freeman’s Cydia store for jailbreak-iPhone apps continues to point the way forward. His Cydia Installer remains an organizing tool for frustrated developer creativity, linking to app repositories that have proved to be useful crystal balls for predicting future Apple iPhone OS enhancements.
“I definitely believe [Apple’s] decisions increase the demand for Cydia: Developers want to be able to improve on the base platform, and Apple doesn’t let them even come close to that,” says Freeman.
Of the jailbreak iPhone apps we listed last year, more than half still can’t be implemented on all native iPhones. Still thriving in Cydia, these apps and several new offerings show promise as future Apple enhancement prototypes. (See “21 apps Apple doesn’t want on your iPhone 3.0”).
Recent jailbreak apps of note include those that streamline background task management, such as Multifl0w, which helps users switch between multitasking apps in a way similar to how app switching is performed on Android handsets. Another popular category is personal Wi-Fi hotspot creation, as illustrated by MyWi. Several apps, such as QuickReply, exploit background processing to let users pop out of an app to, for example, reply to a message, then return to where they left off.
Security has become an important issue for iPhone users, both due to demonstrated vulnerabilities inadvertently created during jailbreaking and as a result of privacy liberties taken by traditional app vendors, such as Facebook. Firewall iP is an app that addresses this interest; it helps users stay in control of their data by alerting them to any unusual outbound data transmissions.
Apple iPhone sales—and jailbreaking—to continue
Despite numerous “end of jailbreaking” scares, the iPhone DevTeam and compatriots have so far always succeeded in sawing through any bars and locks Apple adds with each new OS release. Thousands, if not tens of thousands, of these users are non-AT&T subscribers, which add to Apple’s bottom line, to AT&T’s chagrin.
The jailbreaking phenomenon also likely presages a similar movement in the nascent Apple iPad community. The iPad, what many see effectively as a giant iPod Touch, runs iPhone apps natively and may also be crackable by iPhone escape artists.
It’s safe to say that as long as Apple maintains its heavy-handed grip on “authorized” iPhone developers, jailbroken phones, and app stores such as Cydia, will continue to thrive, even after the iPad arrives.
This story, “Jailbreaking in the iPhone 3.0 era,” was originally published at InfoWorld.com.
Reblogged via Mel Beckman, InfoWorld.
5:10am, 2 March 2010.
Photoshop and Photography: When Is It Real?
In the March issue of Popular Photography magazine, the editor’s note, by Miriam Leuchter, is called “What Is a Photograph?”
You’d think that, after 73 years, a magazine called Popular Photography would have figured that out. (Ba-da-bump!)
Actually, though, the editorial is about the magazine’s annual Reader’s Photos Contest. This year, in two of the categories, the winners were what the magazine calls composites, and what I call Photoshop jobs.
One photo shows a motorcyclist being chased by a tornado; another shows a flock of seagulls wheeling around a lighthouse in amazingly photogenic formation. Neither scene ever actually existed as photographed.
Now, in my experience, photographers can be a vocal lot. And a lot of them weren’t crazy about the idea of Photoshop jobs winning the contest.
I have to admit that when I saw the winners revealed in a previous issue, I was a bit taken aback, too. I mean, composition and timing are two key elements of a photographer’s skill, right? If you don’t have to worry about composition and timing, because you can always combine several photos or move things around later in Photoshop, then, well — what is a photograph?
The thing is, though, this isn’t necessarily an open-and-shut case. Ms. Leuchter’s editorial points out that photography has never been strictly a “capture reality” art form. It’s never been limited to reproducing what the eye sees.
From the very beginning, photographers have set up their shots, posed people and adjusted brightness and contrast in the development process. So although you may think that some line has been crossed, it might not be so easy to specify exactly where that line sits.
Here’s a list of things people do to and for photographs, ranging from the innocent and traditional to the dangerously artificial. If you were running a photography contest, at what point would you draw the line and say “That’s not photography anymore?”
* You move the camera to get the best possible shot.
* You attach a lens that takes in a much wider or closer view than you would get with your eyes alone.
* You choose a shallow depth of field, providing that sharp-subject, blurry-background look of professional photos, which looks nothing like reality.
* You set up lights to illuminate a scene in a way that nature never intended.
* You bring in a professional crew to transform a model’s skin, clothing and hair.
* You witness a spectacular event, and then ask the people involved to go back and re-enact what just happened so you can have your camera ready.
* In the darkroom, you “burn” and “dodge” to make certain parts of the photo brighter or darker.
* You bring the photo into Photoshop to remove red-eye. (After all, the red-eye wouldn’t have existed if you hadn’t taken the photo to begin with.)
* You bring the photo into Photoshop to make the colors “pop” a little more.
* You bring the photo into Photoshop to shift one element slightly for better composition.
* You combine two or more photographs of the identical scene, taken at different exposures, strictly to produce a better range of lights and darks (what’s called “high dynamic range” photography).
* You combine two or more elements of different photos of the same scene, taken around the same time, simply to get them all in the frame at once (like the seagulls/lighthouse photo).
* You combine two or more elements of different photos that were taken at different times and places (like the motorcycle/tornado photo).
* You use a 3-D modeling program to create a photorealistic scene that never existed anywhere but in your imagination.
Of course, your answer may be something like, “It depends on the purpose of the photo.” If you’re a news photographer, you (and your audience) would probably be O.K. with tweaks to the color and contrast, but that’s it. On the other hand, if you’re an advertising photographer, you and your audience would probably have no problem with anything on the list above.
The question here is, what should the rules be for a photo competition?
Ms. Leuchter suggests that next year, they’ll have a separate category for Photoshop creations. I think that’s a good idea.
But meanwhile, we live in an age where Photoshop jobs are commonplace, reality TV shows dominate the airwaves, and news bites are taken out of context and manipulated. Maybe, these days, the question isn’t “What is a photograph?”; it’s “What is reality?”
Reblogged via Pogue’s Post of NYT
5:20am, 26 February 2010.






leave a comment